With each passing month there is inevitably a new round of malware to combat. With that in mind, I have put together a USB key with the tools I go into battle with against these vicious foes. Your toolkit and mileage may vary. However, this is the kit I’ve used with great success to combat the various threats I’ve found in the Windows world.
First, if you do encounter a machine you can’t access the Windows installation on through Safe Mode of any command line access, go straight to your bootable Windows environment. In my case, I have burned a copy of the Ultimate Boot Disc to CD so I can boot into a familiar Windows environment and access hard drives or network resources if all else fails. This is usually a last-ditch attempt to access and retrieve data off an infected hard drive.
Once I have accessed Windows, I run Autoruns. This will give you a look into every single process, service, and application currently running on the machine. Autoruns shows you the entry (application/service/registry key), description if there is one, Publisher, and the path to the entry. This is invaluable to finding applications that launch on startup. The application 67hklzfrh.exe with no Publisher running in a temp folder is a giant red flag.
ProcessExplorer is a great companion to Autoruns because it will give you far more detailed information about each process running on your computer. If you’re unfamiliar what an application or process is, fire it up. It also had a target icon you can click and drag over an application and it will show you which process corresponds to it. This can be particularly useful if you can’t figure out what process is spawning your pop up windows.
Once I have stopped any auto running applications, I move on to CCleaner. If I can, I clear the caches of each browser on the computer first, but even if that’s successful, I move to CCleaner and blow away all the temporary, cache, and unneeded information on the computer. Anywhere malware can hide; I will find and remove it. It also helps to clean up the caches and temp folders.
From there, I bring in the artillery, SuperAntiSpyware. It has been my experience that if there is a threat on your computer, this program will find and eliminate it. There is also an excellent portable version that runs as a .com file to evade any malware shutting down access to .exe files.
Make sure to update to the latest available definitions before you begin as the portable version does not come preloaded with any definitions at all. Then start your scan and sit back. Your time will vary. Allow at least an hour for the scan to fully run. It will pop up and alert you when it is ready to remove the threats and offer to reboot.
Once you’re shut down the offending applications and run your full malware scan and rebooted, I suggest rebooting back into Safe Mode and checking AutoRuns again and seeing if anything looks out-of-order. From there you can decide if you want to reboot normally and verify the threats are gone. If so, I would recommend rebooting into an account without administrative rights. This will prevent some things from reinstalling themselves if the threat isn’t all gone.
Recently, I worked on an infected computer that hadn’t had Windows Updates run since 2008. AutoPatcher is invaluable in this situation. Once launched, you tell it which version of Windows you’re running and it will go out and collect all the updates it needs, download them, and install them saving you multiple reboots and trips to the Windows Update site. This made the 120+ updates I had to install far more tolerable than if I had used Windows Update.
So far, I have only encountered one PC I could not get into because the spyware had taken it over entirely. I could not boot into Windows, access it in Safe Mode, even booting to an external CD did not work. In that instance, I had to wipe the hard drive and reimage it.
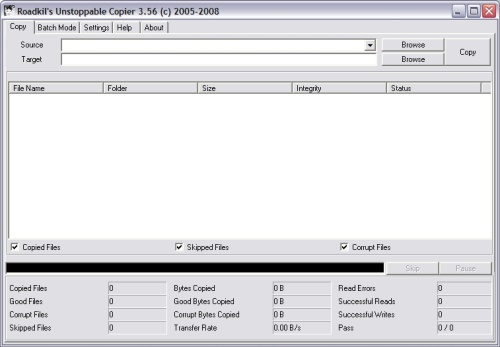
Now that your mission changed from removal to recovery this is when I reach for Unstoppable Copier. Using the standard Windows copier can run into troubles when it hits a file it can’t move it quits or it may hang of fail to write. Then you’re left without any idea of how much data you got. Unstoppable Copier will move data from A to B but with the added benefit of logging each file it moves and skipping locked files so you can get through moving a user’s data without multiple failures. Once it completes, just go back and consult the log for any files it did not move and determine if they’re important or not.
This is what I use to combat malware and spyware in my daily life as an IT Support Technician. Let me know if it works for you or if you’ve found something better. And if you have any questions, ask away.